via www.wired.com

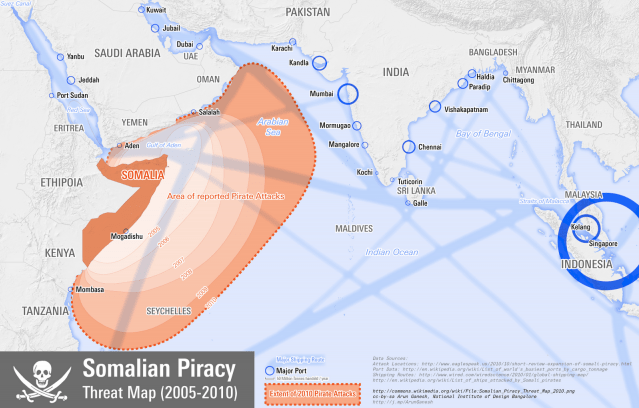
Ransoms paid to Somali pirates averaged $5.4 million last year, compared with $150,000 in 2005, according to One Earth Future, a non-governmental organization based in Louisville, Colorado. A total of $238 million was paid out in 2010, the group said in a report, estimating the annual cost of piracy at $7 billion to $12 billion. That includes ransoms, insurance premiums, re-routing ships, security equipment and naval forces.
Somali pirates still held 28 ships and 638 hostages as of Dec. 31, the IMB said. Pirate attacks also took place in Nigeria and Bangladesh and Indonesia reported its highest level of attacks on ships since 2007, the IMB said. (via Pirates Hijacked a Record Number of Ships and Crew Last Year, IMB Reports – Bloomberg)
Read moreRead moreThe case against WikiLeaks is absolutely this decade’s version of the Saddam/WMD campaign. It’s complete with frivolous invocations of Terrorism, grave public warnings about National Security negated by concealed information, endlessly repeated falsehoods, a competition among political and media elites to advocate the harshest measures possible, a cowardly Congress that (with a few noble exceptions) acquiesces to it all on a bipartisan basis and is eager to enable it, and a media that not only fails to subject these fictions to critical scrutiny, but does the opposite: it takes the lead in propagating them. One might express bewilderment that most American journalists never learn their lesson about placing their blind faith in government claims, but that assumes – falsely – that their objective is to report truthfully.
Read more** Underlying Causes **
This 21st century digital revolution is not driven by irreconcilable tribalism, religion, abuse of human rights or gender.
This is about corruption, extremely high unemployment, out-of-control food and fuel prices and the disruption of the daily lives of ordinary people.
Read moreThere’s a special irony when Google CEO Eric Schmidt suggests—as he did in a speech to the Council on Foreign Relations last November—that China’s government will find it impossible to censor “a billion phones that are trying to express themselves.” Schmidt is rich because his company sells precisely targeted ads against hundreds of millions of search requests per day. If Google can zero in like that, so can China’s censors.
Calling China’s online censorship system a “Great Firewall” is increasingly trendy, but misleading. All walls, being the creation of engineers, can be breached with the right tools. But modern authoritarian governments control the web in ways more sophisticated than guard towers.
This isn’t just theory. The Kremlin is allegedly soliciting proposals for data-mining social networking sites. The police in Iran and Belarus reportedly browse such sites in order to find connections between opposition figures and dissidents. China tried to launch Green Dam, a technology that studies the browsing habits of its users before deciding to block access. And contrary to what Eric Schmidt believes, authorities do have the ability to locate and monitor mobile phone users, as well as censor their messages.
Why all the tricky techniques? Superpowers like China have to engage with the global economy. So for them, the best censorship system is the one that censors the least. Millions of people already disclose intimate social data on Facebook, LinkedIn, Delicious, and their Russian and Chinese alternatives—and that’s all the data governments need to pick the right target. Online friends with an antigovernment blogger? No access for you! Spend most of your day surfing Yahoo Finance? Browse whatever you want. Satisfied Chinese investment bankers will have access to an uncensored web; subversive democracy activists get added to the government watch list.
Can the Internet empower dissidents and pro-democracy activists? Yes. But it can also strengthen existing dictatorships and facilitate the control of their populations. Washington’s utopian plan to liberate the world one tweet at a time could also turn American innovation into a tool for the world’s subjugation.
Make no mistake: what is at stake here is the infrastructure for our national conversation—the very lifeblood of American democracy. We should be moving in precisely the opposite direction of what this Commission approves today
– FCC Commissioner Michael Copps
“Cable-ization of the open Internet”: Comcast/NBCU deal approved
Andrei Zmievski, a San Francisco software engineer, asked Twitter in 2008 to let him claim the handle @A. After he took over the dormant account, he discovered the downside: Whenever a Twitter user enters @ plus the letter A—"I’m @a bar"—the tweet fills Mr. Zmievski’s feed.
The cool name has rendered part of Twitter’s function “useless,” Mr. Zmievski says. “It’s the price I have to pay.”
Single-Name Social Media Handles Are Totems in the Tech World – WSJ.com
hahahahahahahahahahahahaha douche

From imprisoned Pirate Party member to government leader, it’s been an eventful week for Tunisian blogger and software developer Slim Amamou. (via Jailed Pirate Party member becomes Tunisian government minister)
Read more